The search was never the problem
Finding something specific on the internet is easy. Finding something you can trust, from people who know what they're talking about, on a topic where you don't yet know enough to filter the good from the bad: that's a different problem entirelyBE.
For cybersecurity professionals, this is a daily reality. The content exists. There's no shortage of videos, talks, and tutorials. But it lives scattered across YouTube, conference websites, and personal channels, mixed in with sales pitches, outdated tutorials, and beginner content that looks identical to expert content until you're twenty minutes in. A security engineer trying to get up to speed on a specific topic might spend thirty to sixty minutes across multiple platforms, doing the curation work themselves, often settling for something incomplete. Their goal is to protect systems and people. The time spent filtering noise is time taken away from that.IE
A cybersecurity engineer with over a decade in the field came to Tarmiga with that frustration. Not a fully formed product idea: a problem. He couldn't easily find trustworthy video content on specific topics in his field. His experience told him that if someone with his background and network hadn't found a solution, it probably didn't exist yet. My job was to find out exactly what was missing, and what it would take to build it.BE.
From a frustration to a brief
Before any design work began, I built a structured process to make sure we were solving the right problem. I presented a project proposal within three days of our first meeting: two strategic workshops, a market research phase, and a clear plan for what would follow. We had our first workshop five days after our first conversation.UX.
Roadmap Definition
The first workshop focused on two questions: who exactly are we building this for, and what do they actually need? I came prepared with structured interview questions designed to draw out the client's deep knowledge of his own community, because their ten years inside cybersecurity is a research asset. We mapped three distinct user profiles, defined the problem in concrete terms, and set the goals and requirements the product would have to meet. With that clarity, I could begin the research phase knowing exactly what I was looking for.IE.
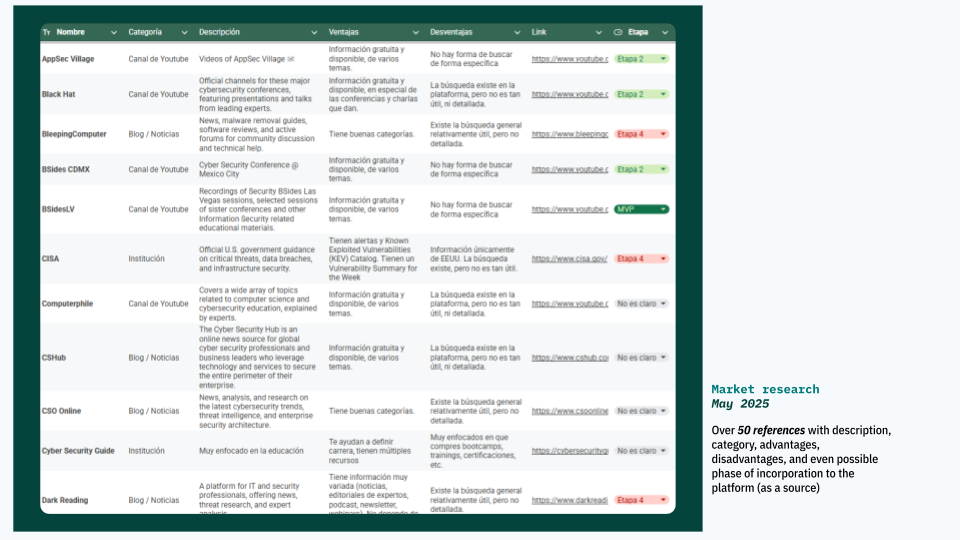
I audited over fifty platforms: YouTube channels, podcasts, blogs, institutional sites, and communities across Latin America and the US. The finding was consistent across all of them: earch exists everywhere. But it is not specific to cybersecurity video content, not built for retrieval, and not designed for the moment when a professional needs to find something trustworthy, fast. Every platform was built for a different primary purpose. Cybersecurity professionals were working around them, doing the curation work themselves.BE.
Market Audit
The second workshop, in late June, sharpened the problem definition further and translated it into a concrete product direction: priorities, features, tagline, distribution strategy, and community touchpoints. By the time design work began in earnest, the problem was no longer a frustration. It was a specification.IE.
A place, not just a platform
The naming research is where the direction became clear.
Naming & Visual Rationale
Cybersecurity engineers are, professionally, exceptional at finding things. They navigate documentation, repositories, and technical directories as a matter of course. That instinct is trained into the work. What struck me was that this same behavior, the habit of going to a structured, trusted place for exactly what you need, had no equivalent for video content in their field. They weren't failing to search. They were each doing their own searching process, because there was no easier pathBE.
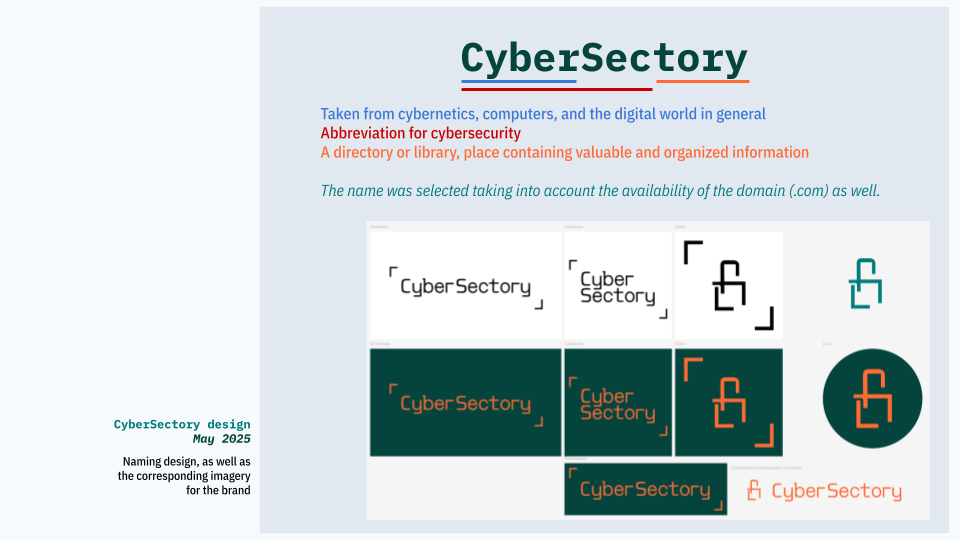
The name came from two words that software engineers know instinctively: directory and library. Both are structured, trusted, and physical in their original meaning. A place you go to find something specific, where someone has already done the organizing for you. CyberSectory: CyberSecurity plus that idea of a place. The concept and the identity arrived together, which meant every subsequent decision had a clear answer to check against: does this make it more like a trusted place, or less?
Built for three different types of people
With the concept clear, the design decisions followed directly from the behavior research rather than from conventionBE. Curation as a product decisionUX means every structural choice is answerable: why this format, why this color, why this navigation path.
The first decision was format. The obvious options were a social media profile, a list, or a community platform like Discord. Each failed for the same reason: none of them were designed for retrieval. Social media surfaces what's recent or popular, not what's relevant to a specific need. Lists exist in abundance and add nothing without curation and structure. Discord is a conversation tool, not a reference tool. A website was the only format that could support the kind of navigation the content required, and the kind of identity the community deserved. We created a social media presence eventually, but as a distribution channel, not as the product itself.
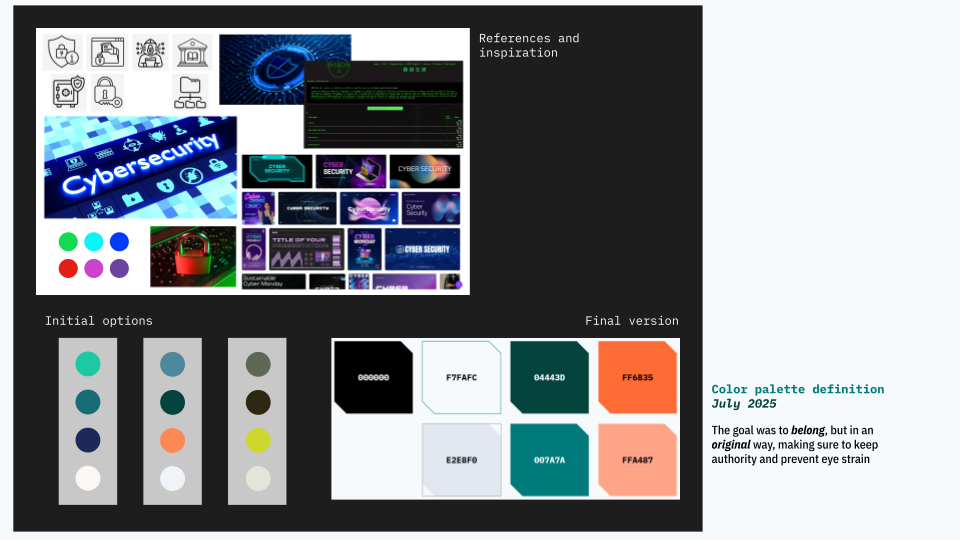
The second decision was color. Cybersecurity design defaults to dark backgrounds, blue and purple palettes, and high contrast. The aesthetic signals expertise but creates visual fatigue for anyone spending real time reading and browsing. CyberSectory was designed for time on site, not for a first impression. Warm backgrounds, readable typography, comfortable contrast. A place you want to stay in, not just arrive at.
Color Palette Design
The third decision, and the most consequential, was navigation architecture. Most content platforms are built for one user type: someone who knows what they want and searches for it. The behavior research had identified three distinct patterns, and the architecture had to serve all three:
- The directed user knows exactly what they're looking for. For them, there is a search bar on the homepage, visible immediately, no scrolling required. Returning users live here.
- The exploratory user has a general area of interest but no specific query. For them, there are broad topic categories on the homepage: OSINT, Red Team, Incident Response, Vulnerability Management, and others. A starting point that doesn't require knowing the right words yet.
- The deep researcher needs precision. For them, there is an advanced search with filters by event, topic, duration, year, and keyword. The same content, accessed with surgical specificity.
Once inside a video, the navigation continues. Every speaker, conference, and topic is a clickable tag. You can follow a thread from a single video outward in multiple directions. Similar videos appear alongside the one you're watching. The architecture assumes that the best next thing to watch is often something you didn't know to search for.
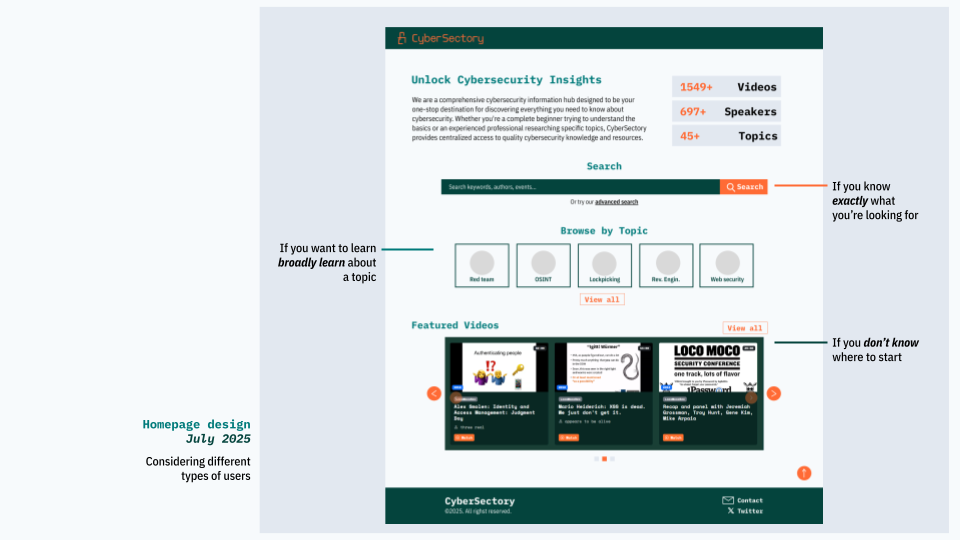
Navigation Entry Points
What was left out is as deliberate as what was built. No recommendations driven by watch history. No algorithmic sorting by engagement. No promoted content. The curation is human and explicit. That is the product decision everything else rests on.
Check it out yourself →Tested in the room where it mattered
The platform went live on August 5, 2025. Within weeks, it was in the hands of real users at DragonJar in Medellín, September 2025, one of Latin America's largest cybersecurity conferences and a deliberate first test environment: the people in that room were exactly the people the platform was built forUX.
The testing was informal by design: attendees were between talks, grabbing food, moving through a busy conference floor. A rigid script would have produced polite answers, not honest onesTL. We approached people directly, let them interact with the platform on their own terms, and asked open questions. Some searched for a specific topic they cared about. Others followed their own curiosity.
What came back was specific enough to act on. Navigation decisions that felt obvious in design felt less obvious in practice. Some paths needed shortening. Some labels needed rethinking. The feedback went directly into post-event improvements to the live product.
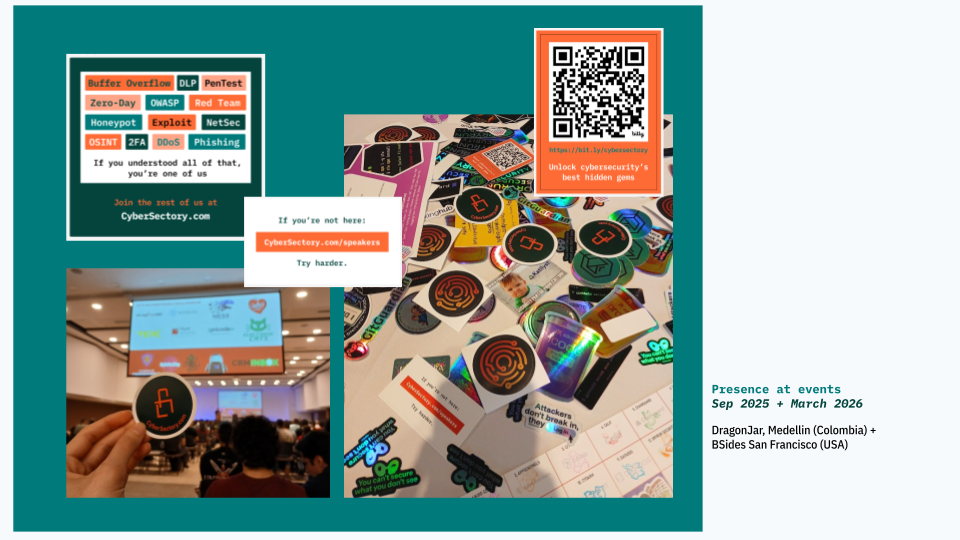
Field Validation in Medellin & San Francisco
The stickers were part of the community strategy from the beginning: a physical artifact designed to signal belonging and extend the platform's presence beyond the screen. We brought them to DragonJar and, months later, to BSides SF in San Francisco. A cybersecurity platform that shows up in the rooms where cybersecurity professionals gather is not just a website. It is part of the community infrastructure.
Less time searching. More time learning.
Before CyberSectory: A security engineer trying to get up to speed on a specific topic opens YouTube, a few conference websites, maybe a community forum. Thirty to sixty minutes later, they have a mix of relevant, outdated, and tangentially related content. They did the curation themselves, because there was no other option.
After CyberSectory: The same search takes only a few minutes. The content is already filtered, the sources are already vetted, and the navigation is built for exactly this moment.
The platform has grown organically since launch, without paid promotion. 1,261+ videos, 1,342+ speakers, 169+ topics. That growth is a signal: the people it was built for recognize it as theirs.
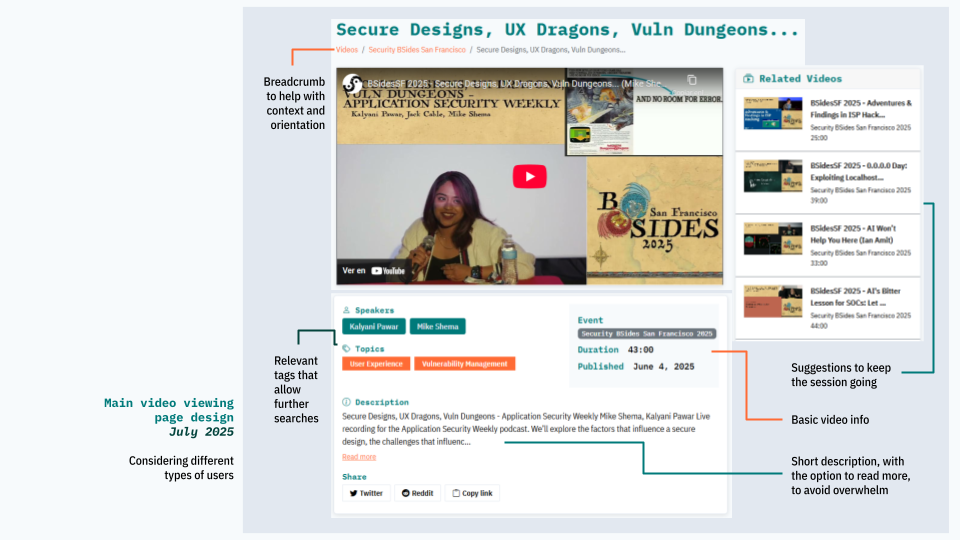
Main visualization screen design
Cybersecurity professionals were already doing the hard work of finding and filtering content. They just shouldn't have had to. The design work here was not about changing their behavior. It was about building the infrastructure IEthat their behavior had always assumed existed.
Reflection
What I learned designing for a domain I knew nothing about before this project is that unfamiliarity is not a liability for a designer. It means you ask the questions an expert has stopped asking, and observe with fresh eyes. I came in not knowing what OSINT meant. I left genuinely curious about social engineering, partly because it sits at the intersection of psychology and systems, which turns out to be exactly where I tend to end up regardless of the domain.
The moment that stays with me is not a design decision. It is a specific look: the instant a user at DragonJar found exactly what they were searching for and registered, visibly, that the platform had understood them. That is what information architecture can do when it is built around behavior rather than around content. And that is the outcome worth designing for.